Privacy Risks in Data Collection and Storage
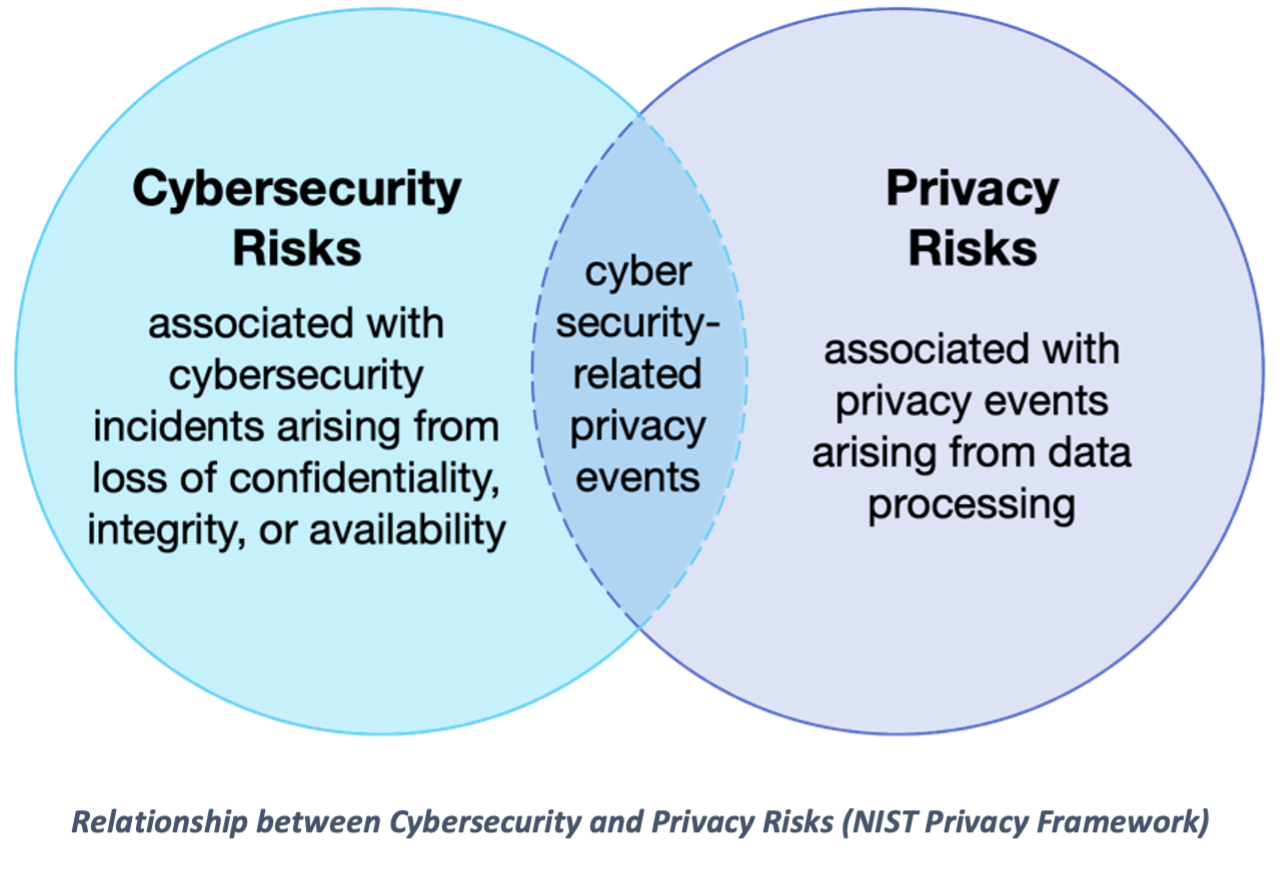
In today’s digital world, companies collect large amounts of personal data from users through apps, websites, and online services. This data can include names, locations, browsing history, and even payment information. While this helps improve user experience, it also creates serious risks if the data is not properly protected.
One major risk is data breaches, where hackers gain access to sensitive information stored by companies. These breaches can expose millions of users’ personal data, leading to identity theft or financial loss. Even large companies can be affected if they do not maintain strong security systems.
To prevent these risks, organizations use encryption, secure servers, and privacy policies. Users can also protect themselves by using strong passwords, enabling two-factor authentication, and being careful about what information they share online.

Example: A company database gets hacked and user passwords are leaked.
Source: https://www.imperva.com/learn/data-security/data-security/
Misuse and Protection of Computing Resources
Computing resources such as computers and networks can be misused by hackers for harmful purposes. One example is malware, which secretly takes control of a device to perform unwanted actions like sending spam or mining cryptocurrency.
Another form of misuse is botnets, where many infected devices are controlled to launch attacks on websites. These attacks can overload systems and cause services to shut down temporarily.
A real world example is when In 2016, a former Google employee, Anthony Levandowski, downloaded thousands of confidential Project Chauffeur files onto his personal laptop before joining Uber. This insider misuse of computing resources caused legal disputes and highlighted the importance of monitoring and protecting sensitive company data.

Example: Malware uses your computer without permission to perform tasks.
Source: https://www.cisa.gov
Unauthorized Access to Information
Unauthorized access happens when someone gains entry to data or systems without permission. Hackers use methods such as phishing, password guessing, and exploiting software vulnerabilities to gain access to unauthorized data.
Phishing is a common method where attackers send fake emails to trick users into entering personal information. Many breaches occur because users are unaware of these scams.
To prevent unauthorized access, companies use encryption and multi-factor authentication. Users should also create strong passwords so hackers aren't able to guess your password easily, and don't click on links that seem suspicious.

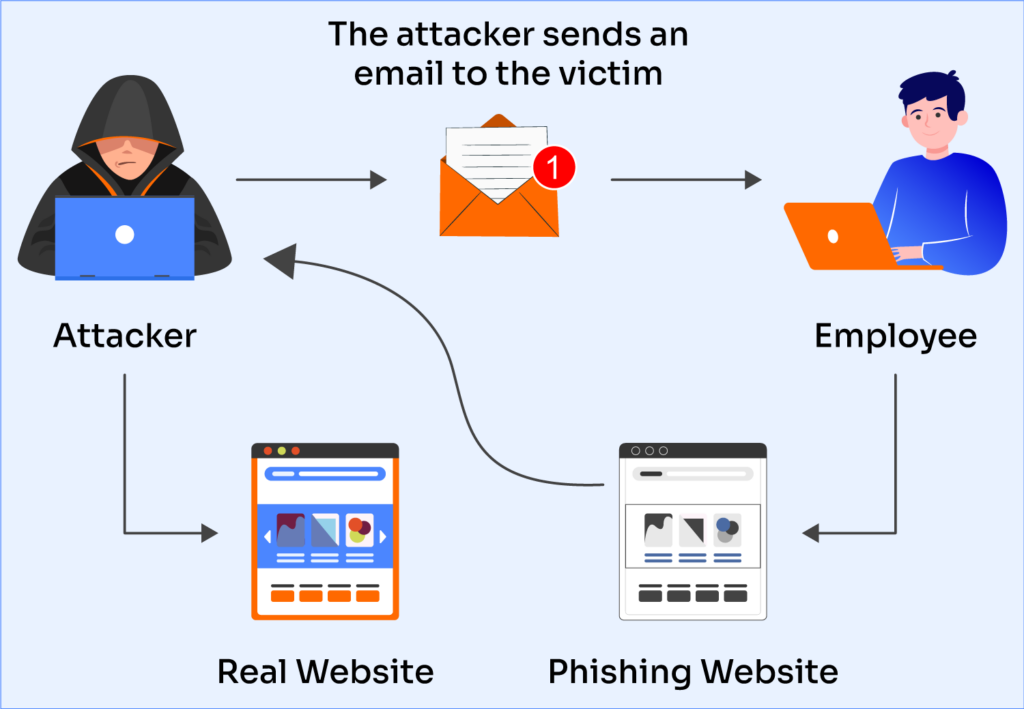
Example: A fake email tricks someone into giving away their password.
Source: https://brightsec.com/blog/unauthorized-access-risks-examples-and-6-defensive-measures/
Benefits and Risks of Computing Innovations
Computing innovations such as artificial intelligence and cloud computing have improved many aspects of life. They allow faster communication, better healthcare, and more efficient business operations.
However, these technologies also have risks. AI systems can be biased, and social media platforms can spread misinformation quickly. Some technologies are used in ways that were not originally intended. For example people use AI to make images that people might take it as mockery.
To reduce risks, developers must create technology responsibly and consider its impact. Governments and organizations also create rules to ensure safe and fair use.
Example: AI systems making unfair decisions due to biased data.
Source: https://www.ibm.com/think/insights/10-ai-dangers-and-risks-and-how-to-manage-them